Teetering on the Edge: VPNs, Firewalls' Nonexistent Telemetry Lures APTs
State-sponsored groups are targeting critical vulnerabilities in virtual private network (VPN) gateways, firewall appliances, and other edge devices to make life difficult for incident responders, who rarely have visibility into the devices.
April 23, 2024

Earlier this year, Mandiant Consulting's incident response team tracked an attack by a China-linked espionage group back to the compromise of an edge device in its client's network, but because the appliance is a closed system, the victim of the attack had to request a forensic image from the maker of the network appliance.
Two months later, the client is still waiting.
This difficulty in detecting — and then investigating — compromises of edge appliances highlights why many nation-state attackers are increasingly targeting firewalls, email gateways, VPNs, and other devices, says Charles Carmakal, CTO for Mandiant Consulting at Google Cloud. The threat groups not only evade detection longer, but even when defenders get wind of the attack, investigating the incident is much more difficult.
It's a problem that Mandiant deals with "all the time," he says.
"We have much better telemetry for Windows computers today, mostly because of the maturity of EDR [endpoint detection and response] solutions," Carmakal says. "The telemetry on edge devices ... is often completely nonexistent. To be able to triage and forensically examine the device, you've got to get a forensic image, but you can't just open up the device and pull the hard drive out."
Espionage attackers' shift to exploiting edge devices is one of the major trends that Google Cloud's Mandiant Consulting saw in 2023, according to the M-Trends 2024 report published on April 23. Overall, the company tracked and reported on more than two dozen campaigns and global events in 2023 related to its investigations.
The amount of time an attacker is active on a compromised systems before detection, known as dwell time, continued to shrink — to 10 days in 2023, down from 16 days the previous year. Ransomware accounted for 23% of Mandiant's investigations in 2023, up from 18% in 2022. Companies became aware of most incidents (54%) because a third party — often the attacker themselves, in the case of ransomware — notified the victim.
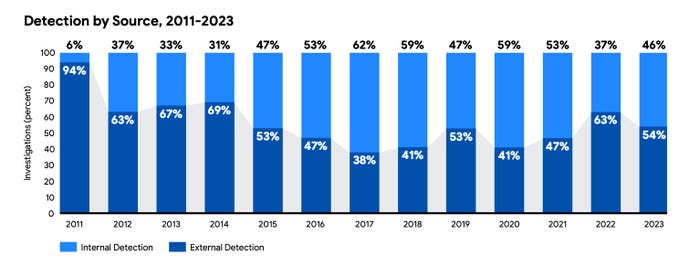
With ransomware often notifying victims, external detection rose to 54%. Source: Google Cloud's Mandiant
Attackers Move to Less Visible Environments
While edge devices require knowledgeable attackers to compromise and control them, these high-availability environments also usually offer their own utilities and features to deal with native formats and functionality. By "living off the land" and using the built-in capabilities, attackers can build more reliable malware and still run less risk of being detected, because of the lack of visibility defenders have into the internal operations of the devices.
"[M]any of these devices are put through rigorous testing regimes by the manufacturer during development to ensure their stability," Mandiant stated in the report. "China-nexus malware developers take advantage of the built-in functionality included in these systems ... leveraging native capabilities [that can] reduce the overall complexity of the malware by instead weaponizing existing features within that have been rigorously tested by the organization."
In one incident, Mandiant consultants discovered the BoldMove backdoor malware, Chinese attackers crafted to infect a Fortinet device, disabling two logging features and allowing the attacker to remain undetected for a longer period. BoldMove was created specifically for Fortinet environments.
Incident response efforts are also often hampered by the lack of easy access for consultants and defenders to the underlying operating system. With no way to analyze the underlying code to seek out compromised devices, incident responders often cannot determine the root cause of a compromise, says Mandiant's Carmakal.
"Some vendors refuse to give forensic images, [which] I understand ... because they have a lot of intellectual property on the device," he says. "Companies need to understand the scope and extent of a compromise, and if it starts on a network device, and you need to look into that."
Exploit Use Rises, More Data Leak Sites
Attackers have doubled down on using exploits as the initial access point for attacks, with 38% of attacks Mandiant investigated where it could determine an initial vector starting with an exploit. Phishing, a distant second place, accounted for 17% of the initial actions in an attack. Running a close third, prior compromises inadvertently left exploitable accounted for 15% of all initial access vectors.
"Attackers continue to leverage effective tactics to gain access to target environments and conduct their operations," the Mandiant report stated. "While the most popular infection vectors fluctuate, organizations must focus on defense-in-depth strategies. This approach can help mitigate the impact of both common and less frequent initial intrusion methods."
Finally, Mandiant investigators have also seen data leak sites (DLS) increase over time, which now account for more than a third (36%) of all financially motivated attacks.
About the Author(s)
You May Also Like
Key Findings from the State of AppSec Report 2024
May 7, 2024Is AI Identifying Threats to Your Network?
May 14, 2024Where and Why Threat Intelligence Makes Sense for Your Enterprise Security Strategy
May 15, 2024Safeguarding Political Campaigns: Defending Against Mass Phishing Attacks
May 16, 2024Why Effective Asset Management is Critical to Enterprise Cybersecurity
May 21, 2024
Black Hat USA - August 3-8 - Learn More
August 3, 2024Cybersecurity's Hottest New Technologies: What You Need To Know
March 21, 2024




