DanaBot Banking Trojan Is Now Finding Its Way to the US
The DanaBot Trojan first targeting organizations in Australia earlier this year has expanded into Europe and now is aiming at US, according to Proofpoint.

A banking Trojan that was discovered earlier this year and targeted organizations in Australia has made its way across Europe and now is being used in campaigns in the US, according to researchers with cybersecurity vendor Proofpoint.
In September, researchers found a campaign based on the DanaBot Trojan that was using hundreds of thousands of email messages that were aimed at recipients in the US.
It appears that this campaign was being run by the same threat actor who has used the Panda banking Trojan in daily campaigns in the US. Then, for at least a day, the cyberciminal switched to DanaBot.
The appearance of the DanaBot Trojan illustrates how quickly a formidable piece of malware can be adopted and enhanced by other bad actors and expand its reach, according to Chris Dawson, threat intelligence lead at Proofpoint. It also points to the continued and growing popularity of banking Trojans among attackers as a way of gaining quick access to a lot of money. (See Kronos Returns as Banking Trojan Attacks Ramp Up.)
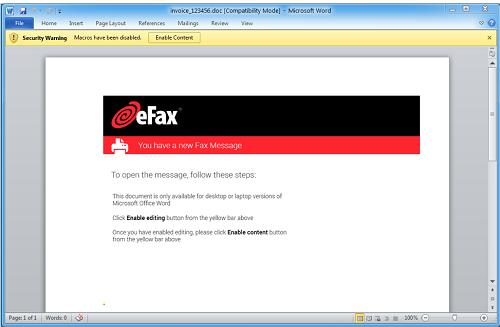
Corrupt email that is part of the DanaBot campaign
\r\n(Source: Proofpoint)\r\n
"The actor we first associated with DanaBot's distribution in Australia is noted for purchasing banking Trojans from other developers and operators, suggesting that DanaBot would be available for sale more widely to other threat actors soon," Dawson told Security Now in an email. "Moreover, DanaBot's anti-analysis capabilities, updated stealer, and remote control modules likely caught other threat actors' attentions, sparking the global distribution that we've observed."
Proofpoint analysts first discovered DanaBot in May and tied it to a single actor who was eyeing victims in Australia.
Quickly campaigns using DanaBot were discovered by ESET researchers in Germany, Austria, Italy and Poland, while Proofpoint detected additional campaigns in Australia. On September 26, a campaign in the US was seen using an eFax in email messages as the lure for victims. It contained a URL that led to the downloading of a document that contained malicious macros that, if enabled by the user, put the embedded Hancitor malware into play. That malware would contact the command-and-control server and then download two versions of Pony Stealer and the DanaBot malware.
DanaBot is written in Delphi and includes the loader, main component that downloads, configures and loads modules, and the modules themselves, which contain various malware capabilities.
"DanaBot includes a significant amount of junk code including extra instructions, conditional statements, and loops," the Proofpoint researchers note in a blog post. "When combined with the use of Delphi, these features dramatically impair reverse engineering. In addition, DanaBot uses Windows API function hashing and encrypted strings to prevent analysts and automated tools from easily determining the code’s purpose."
They wrote that they didn't have great visibility into DanaBot's C&C infrastructure, but noted that the main component of the Trojan contains a list of ten, hard-coded C& IP addresses used for malware communications. Those lists changed about every hour when the main component was downloaded, which told the analysts that Danabot "follows in a long line of malware from one particular group. This family began with ransomware, to which stealer functionality was added in Reveton. The evolution continued with CryptXXX ransomware and now with a banking Trojan with Stealer and remote access functionality added in Danabot."
The popularity of DanaBot is not a surprise, given the rising interest among threat actors in banking Trojans in general. Proofpoint's latest quarterly report found that the banking Trojan was the most popular type of malware the second quarter this year, accounting for 42% of malware detected. In their own second-quarter report, Kaspersky Lab researchers found similar trends, with the rise of mobile banking Trojans fueled in part by modifications aimed at helping the malware evade security tools. In all, Kaspersky researchers found 61,045 installation packages for mobile banking, three times the number seen in the first quarter. (See Banking Trojans on the Rise in Q2, Kaspersky Report Finds.)
"Cybercriminals follow the money and banking trojans allow threat actors to literally remove funds from a target's bank account, providing instant financial gain," Dawson wrote. "Contextually, our data sees significant targeting of commercial enterprise bank accounts rather than consumer checking accounts due to the significant difference in funds. Threat actors typically leverage banking Trojans to access large payroll accounts, accounts used to pay for inventory, and other accounts that have significant amounts of corporate funds available to steal."
The fact that such Trojans usually run on the client side with man-in-the-browser kind of attacks makes it difficult for banks to address them beyond implementing multi-factor authentication, he said.
"Instead, organizations and individuals are considered the front line of defense against banking Trojans," Dawson added. "As with other types of malware, multilayered defenses at the email gateway, the network gateway, and the endpoint, along with strong user education programs, are all critical for organizations looking to prevent infections with banking Trojans."
Related posts:
— Jeffrey Burt is a long-time tech journalist whose work has appeared in such publications as eWEEK, The Next Platform and Channelnomics.
Read more about:
Security NowAbout the Author
You May Also Like




