From Vicious To Virtuous: A Plan Of Attack For Incident ResponseFrom Vicious To Virtuous: A Plan Of Attack For Incident Response
How do you get there? Increase the cost and effort required by the bad guys and boost your efficiency.

Post-audit, post-breach, post-I-just-started-a-new-job, you know you should boost your incident-response efforts and may wonder where to invest. In a new SANS survey on incident response, co-sponsored by Intel Security, the top impediments to IR success were predictable, with shortage of skills and budget for tools and technology leading the list (see chart below).
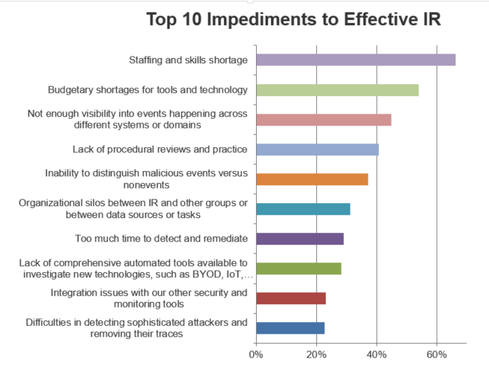
Overall, there’s a correlation between many of the top 10 impediments. For example, a company’s visibility across events and domains and its ability to discern malicious from benign events would both be improved if it had the right tools and technology. This is a vicious circle.
How do you get off this hamster wheel? Through two strategies:
Increase the cost and effort required by the bad guys
Increase your efficiency
Harder For Them
First, make the bad guys lives’ difficult. For example, in a survey at Black Hat 2015, we asked where people were struggling most today across the attack chain (see chart below).
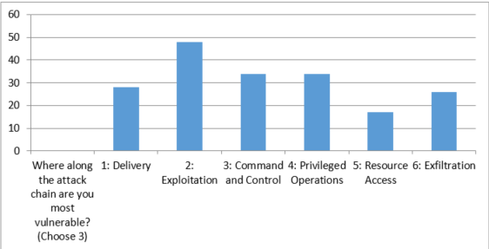
Mitigation of the number one challenge -- exploitation -- requires reducing the attack surface, not just structurally as you might with controls such as application whitelisting, but in an ongoing way with active vulnerability management.
Incident responders can provide the most valuable insights as to the nature and tactics of attacks and where your specific organizations may be vulnerable. Capturing and sharing that feedback quickly so administrators can refine policies and improve countermeasures can be tremendously helpful in staying on the pre-breachside of the attack timeline. And this effort is selfishly beneficial for incident responders: By raising the bar on protection, fewer security events enter their queue.
Threat-intelligence sharing is another way that you can make the cybercriminal business less profitable. Attackers have to keep moving on, keep evolving, keep investing. For instance, as you discover new malware in your sandbox, use STIX to share its details. In addition, consume select STIX feeds, hunt for those indicators within your infrastructure, and match your internal detections to industry findings to prioritize events (and the utility of external data). These efforts help address the command-and-control and delivery challenges that Black Hat attendees highlighted.
Easier For You
In addition, drive to increase your efficiency. As the SANS survey shows, there are many different opportunities for improvement in both detection and response such as better detection of stealthy maneuvering through expanded visibility and advanced analytics. This survey shows that correlation and anomaly detection are being adopted and having an impact. It aligns with other survey findings about the value of timely data.
Customers tell us they see ROI when they centralize event and threat data, processes, and policy management. They can distill and prioritize events that are most relevant to their organizations (detect the real malicious events), then contain and remediate compromised systems using centralized tools and workflows. These are the challenges the SANS survey respondents highlighted. Together, these strategies shrink dwell time, reduce the costs of attacks, and enhance that virtuous cycle.
About the Author
You May Also Like




