Survey Says: Incident Response Is Fighting Back
Companies appear to be recognizing the need for increased incident-response spending.

Today the SANS Institute released a new incident-response survey that we co-sponsored, with some useful and encouraging findings for practitioners and managers of security operations.
There’s quite a bit of good news. At least in part thanks to the increased integration of correlation and analytics, time to remediation has dropped since last summer. The chart below comparing the two years’ of data shows an overall shift to the left -- an improvement in the elapsed time from detection to remediation.
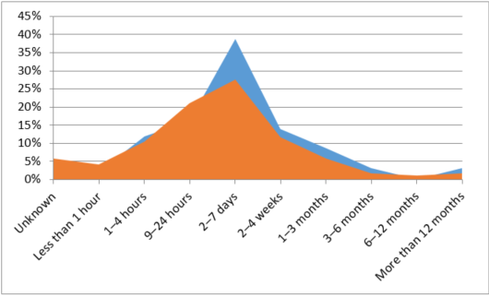
The area in red shows 2015 responses, the area in blue shows 2014 responses to the question: “From the time the incident was discovered, how much time elapsed until remediation was achieved?”
This survey also agreed with findings in other surveys that real-time analytics are helping companies progress. The SANS report says, “A notable 42% of respondents have fully integrated, and 33% have partially integrated SIEM [security information and event management] into their IR ecosystems for analytics during response. Some may also be relying on their CTI [cyberthreat intelligence] tools or services to do the analytics for them, with 26% fully integrating and 28% partially integrating CTI within their functions. The 13% of organizations not currently integrating analytics such as SIEM into their response should consider this a top priority to mature their SOC and IR processes.”
One of the reasons to integrate analytics and SIEM is that centralized tools can accelerate remediation. Even if the decision to remediate needs to involve a human, centralized tools simplify access to and implementation of the right correction. Specifically, centralized tools help more people, including surge resources, get involved in and accurately follow remediation workflows. Automation further improves results. SIEM, EDR, and unified policy management systems are all beneficial ways to centralize and automate approved remediation actions.
Companies appear to be recognizing the need for increased incident-response spending. IR teams should be pleased that the industry is planning increased investments in areas that simplify detection such as correlation and improved visibility into vulnerabilities and threats. (See chart below.)
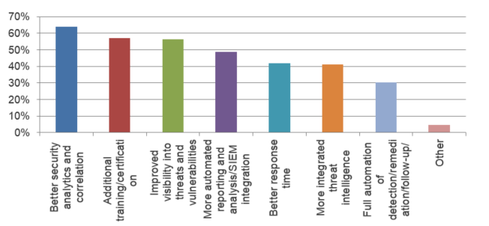
Question: What improvements in IR is your organization planning to make in the next 12 months?
Our work with enterprises shows that these capabilities complement existing SIEM deployments and help companies mature their overall security operations.
Read the survey and see how your team and plans stack up to the industry’s.
About the Author
You May Also Like




