Tricky CAPTCHA Caught Dropping Lumma Stealer MalwareTricky CAPTCHA Caught Dropping Lumma Stealer Malware
The persistent infostealer's latest campaign inserts fake CAPTCHA pages into legitimate applications, fooling users into executing the malicious payload, researchers find.
October 22, 2024
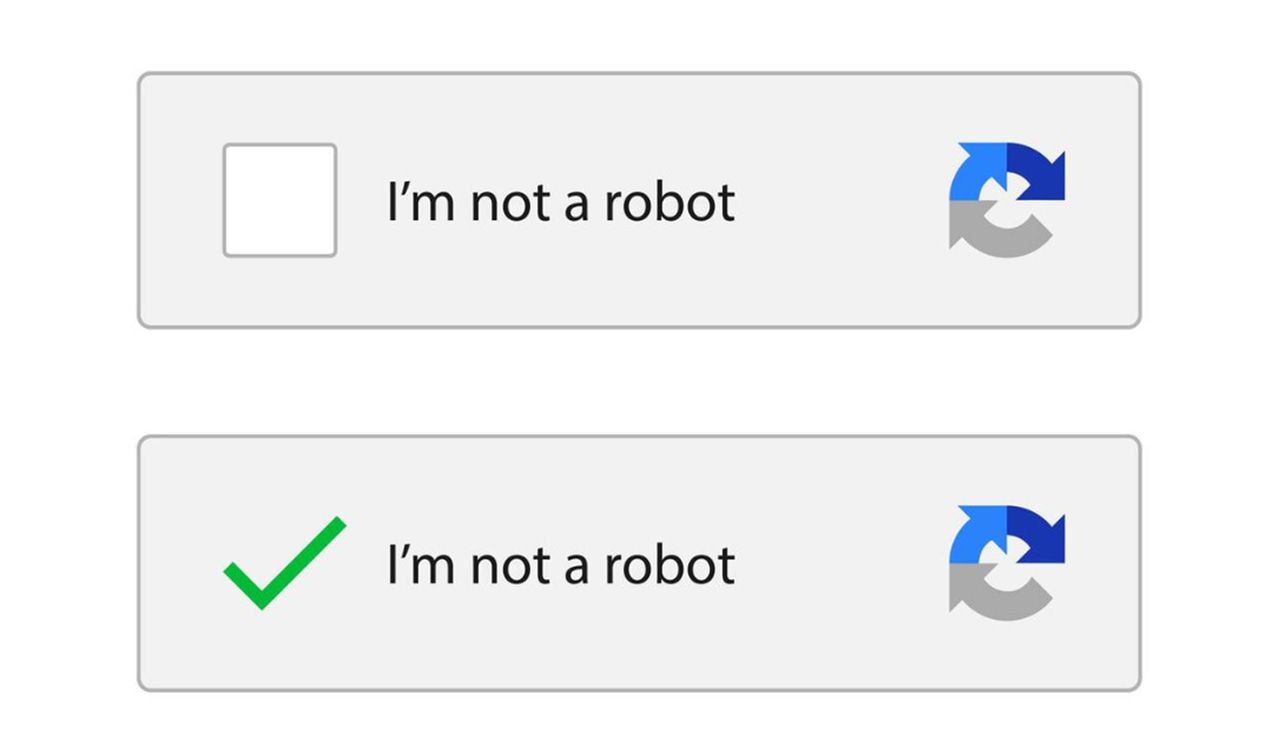
Lumma Stealer stars in a new campaign that uses malicious CAPTCHA pages to scam targets into clicking through the "verification" process — triggering the initial malware download.
Malware-as-a-service (MaaS) Lumma Stealer is commonly used by threat actors to steal sensitive information like passwords and crypto-wallet data, researchers at Qualys, who recently detailed the latest attack chain, explained.
"When the user clicks the 'I'm not a robot' button, verification steps are presented," Qualys threat researcher Vishwajeet Kumar wrote in a blog post detailing the latest Lumma Stealer find. "Completing these steps triggers the execution of a PowerShell command that initiates the download of an initial stager (malware downloader) on the target machine."
Lumma Stealer's Easy Adaptability
This latest CAPTCHA-based tactic is new, Kumar added in the Lumma Stealer campaign analysis. Previous campaigns have relied on a wide array of cybercrimes to spread the infostealer, ranging from basic phishing to far more exotic gambits.
Just a handful of examples from just this year include a Lumma Stealer campaign from January 2024 that used YouTube channels disguised as content to offer workarounds for eluding Web filters and cracking popular applications.
By the summer, another Lumma Stealer effort popped up on Facebook, this time trying to lure victims into downloading a legitimate artificial intelligence (AI) photo editor. Even Hamster Kombat wasn't spared. The more than 250 million estimated players of the game were targeted and lured into downloading Lumma Stealer by multiple simultaneous scams, it was discovered last July.
"The investigation into Lumma Stealer reveals an evolving threat landscape characterized by the malware’s ability to adapt and evade detection," Kumar wrote. "It employs a variety of tactics, from leveraging legitimate software to utilizing deceptive delivery methods, making it a persistent challenge for security teams."
Protecting from ongoing Lumma Stealer threats requires close collaboration between threat intelligence, security operations centers (SOCs), and incident-response teams, according to Sarah Jones, a cyber-threat intelligence research analyst at Critical Start.
"Given the rapid evolution of threats like Lumma Stealer, security teams must adopt a stance of continuous monitoring and adaptation, regularly updating detection rules, indicators of compromise, and security controls," Jones says. "This campaign exemplifies the sophisticated threats organizations face today, requiring a multilayered defense approach that combines advanced technical controls with proactive threat hunting and ongoing adaptation to effectively combat evolving malware campaigns."
About the Author
You May Also Like



_Nils_Ackermann_Alamy_Stock_Vector_.jpg?width=700&auto=webp&quality=80&disable=upscale)
