Why InfoSec Pros Should Keep A Close Eye On Cyber Efficiency
No organization will ever be impervious to breaches, but efficient organizations can lower their overall spend.

The intense demand for trained information security and privacy practitioners is reflective of the convergence of technology, productivity, and profitability. CIOs and CISOs that balk at enabling more mobile, cloud, and Internet of Things (IoT) tools not only find themselves in a cultural conflict, but as more and more devices become IP-enabled, reluctant security practitioners will also find themselves at odds with the business or mission of the organization.
For instance, Boston Consulting Group indicated that the remote cardiac monitoring market in the US alone would eclipse $1 billion in 2016, a specific example of the convergence between technology, productivity, and profitability. The ability for a doctor to remotely adjust a pacemaker without a patient visit or in an emergency situation has a profoundly positive impact on patient care. Information security and privacy practitioners simply must find a way to enable this kind of technology while encompassing the risk as best they can.
At the same time, there is a systemic personnel problem. There are simply far too few trained information security and privacy practitioners available to organizations; the baby boomer generation is taking decades of experience with it into retirement; and the prospects for replacing them are bleak. The 2015 (ISC)2 Global Information Security Workforce Study estimates two global labor gaps: the gap between the existing workforce and what the respondents’ companies are funded to hire (600,000 workers), and the gap between the existing workforce and what those companies believe the need is (1 million further workers). As more devices become IP-enabled for the first time and need to be incorporated into an organization’s information security and privacy posture, the tax upon practitioners will become even more pronounced. Also, for the first time in the (ISC)2 study, practitioners have become acutely aware that the premise that they’ve used for the last 20 years -- buy unique tools for each specific IS and privacy problem -- has created an unwieldy “sprawl in security technologies.”
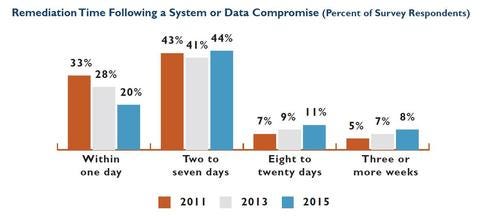
All of these conditions -- demand, expanding IP footprint, convenience, cost reduction, and insufficient trained practitioners -- create an untenable competition between business or mission enablement and security. Evidence of this competition can be seen in the dramatic increase in time from breach detection to remediation. The (ISC)2 study results show a troubling trend indicative of a workforce stretched by demand and sprawl, as indicated in the chart below:
It is for these reasons that dramatic improvements in both efficiency and efficacy should be the goal of any decision IS teams are considering. The ability to get to solid results quickly is the only way that teams can compete with the mathematical problems described above. Any decision regarding methodology, vendor, product, or service that doesn’t demonstrably increase efficiency and efficacy is a bad decision.
Organizations that invest in ensuring that their infrastructure becomes more streamlined, automated, interoperable, resilient, sprawl-reducing, and focused will stay ahead of the math and enjoy the most important results.
No organization will wind up impervious to breaches, but efficient organizations will lower their overall spend by consolidating the number of vendors, tools, and services they use; reduce their labor-hour costs by ensuring automated means of execution; reduce the number of events that operators and analysts need to respond to manually; and shrink the hours operators and analysts spend by reducing events requiring follow-up to fewer, more noteworthy events. The time between breach and detection and the time between detection and remediation will drop measurably, ensuring that breaches don’t have a material effect on the business or mission of an organization.
Over the next few weeks, I’ll explore several techniques that will allow organizations to improve their efficiency and efficacy and reduce the labor hours and per-hour costs associated with operations.
About the Author
You May Also Like




