Most Security Pros Expect to Suffer Cyberattacks via Unsecured IoTMost Security Pros Expect to Suffer Cyberattacks via Unsecured IoT
A new report shows the majority of security professionals believe within the next two years they will be victims of DDoS and other attacks due to unsecured IoT devices.

IT security professionals expect their companies' wireless printers to wireless thermostats and other IoT devices in the next two years to rebel against them in a big way as cyber attackers take advantage of vulnerabilities in the software and devices, according to a report released today by the Ponemon Institute.
The Internet of Things (IoT): A New Era of Third Party Risk report, which surveyed 553 risk management professionals, found that 94% of these security pros believe that in the next two years unsecured IoT devices and IoT applications will likely lead to a catastrophic event; data loss or theft (78%); DDoS attack (76%); and a cyberattack (76%).
As a result, companies need to track third-party IoT devices and IoT software connecting to their network and provide a way to centrally monitor their activities, according to Larry Ponemon, chairman and founder of the Ponemon Institute and the report's author, and Charlie Miller, senior vice president of Shared Assessments, which sponsored the report.
But less than half of the survey respondents say they monitor the risk of IoT devices used in the workplace.
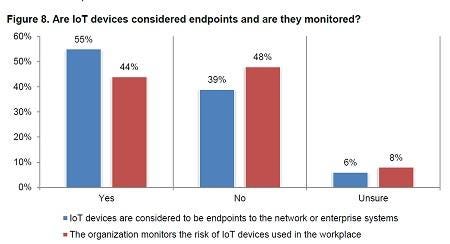
[Charts Source: Ponemon Institute and The Santa Fe Group, Shared Assessments Program]
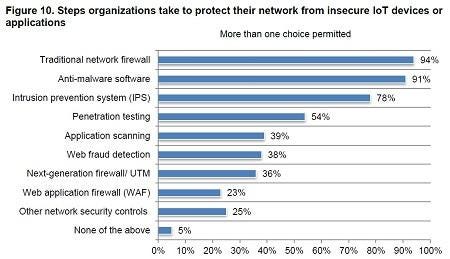
As for holding IoT third-party vendors accountable, Miller suggests it should be addressed in the vendor contract. But he admits that isn't easy: "Many rely on a contractual relationship for security. It is easy to say, but can be difficult to manage."
Ponemon suggests CISOs take several steps toward managing the security risks around IoT third-party devices and software.
"Currently, there are no standards, or processes, or checklists to reduce the risk of IoT," Ponemon says. "One of the first steps is around governance and figuring out who should own the responsibility of unsecured IoT devices and working with the third parties who bring in IoT."
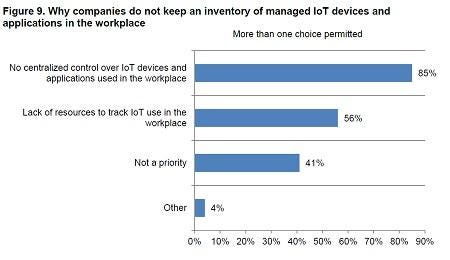
The second step is to take inventory of all IoT tools and relationships that have business risks - like wireless printers or wireless security cameras - and establish IoT categories such as security that would include security cameras, rather than every camera.
And lastly, CISOs should consider creating specific policies and procedures for each category of IoT, Ponemon says. An IoT refrigerator poses a different security risk than an IoT printer, for example.
[Charts Source: Ponemon Institute and The Santa Fe Group, Shared Assessments Program]
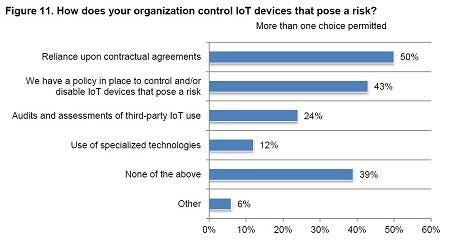
The report also shows that a vast majority of companies use traditional network firewalls and anti-malware software to guard their network from unsecured IoT devices and IoT applications:
[Charts Source: Ponemon Institute and The Santa Fe Group, Shared Assessments Program]
Ponemon says while protecting the enterprise running IoT devices and applications, organizations also must avoid making security so difficult that it stops innovation or interferes with operations.
Related Content:
About the Author
You May Also Like
Uncovering Threats to Your Mainframe & How to Keep Host Access Secure
Feb 13, 2025Securing the Remote Workforce
Feb 20, 2025Emerging Technologies and Their Impact on CISO Strategies
Feb 25, 2025How CISOs Navigate the Regulatory and Compliance Maze
Feb 26, 2025Where Does Outsourcing Make Sense for Your Organization?
Feb 27, 2025




