Supermicro: Report Clears Company of Hacking AllegationsSupermicro: Report Clears Company of Hacking Allegations
Following a Bloomberg report that found hackers implanted specialized chips in its motherboards, Supermicro claims an audit has cleared the company of wrongdoing.

In an attempt to clear the company name, Supermicro released the results of an audit that showed hackers did not compromise the firm's hardware by implanting highly specialized chips that would lead to large-scale industrial espionage.
In a December 11 letter sent to customers, CEO Charles Liang and David Weigand, the chief compliance officer, wrote that after articles appeared in Bloomberg, the company contacted a third party to investigate the allegations in the report. Ever since the story broke, Supermicro has denied the charges, and the analysis looks to bolster those claims.
"A representative sample of our motherboards was tested, including the specific type of motherboard depicted in the article and motherboards purchased by companies referenced in the article, as well as more recently manufactured motherboards," according to the letter published Tuesday. "Today, we want to share with you the results of this testing: After a thorough examination and a range of functional tests, the investigations firm found absolutely no evidence of malicious hardware on our motherboards."
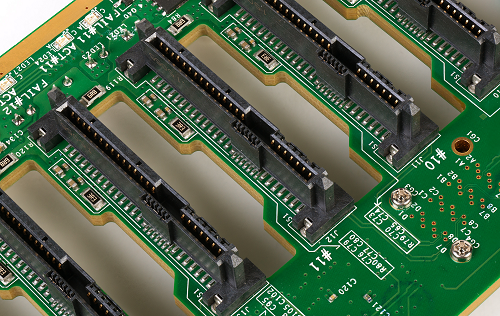
A Supermicro board
\r\n(Source: Wikipedia)
In October, Bloomberg report that a group of hackers infiltrated Supermicro's supply chain and managed to implant tiny microprocessors on the company's motherboards, which were then installed in servers and shipped to customers such as Apple and Amazon Web Services. (See China Hacks Hardware in Spying Attempt on Apple, Amazon & Others – Report.)
This type of hardware hack is nearly impossible to pull off, which led to speculation that a specialized unit within China's People's Liberation Army pulled off the feat.
Almost immediately, the report drew criticism from Apple, AWS, Supermicro and other companies, as well as the US government. (See Bloomberg Hardware Hacking Story Faces Fierce Backlash From Apple & DHS.)
Bloomberg has stood by its reporting.
In an email, Patrick Moorhead, president and principal analyst with Moor Insights & Strategy, noted that, so far, no solid evidence has surfaced that confirms the hardware hacking allegations.
"What was laid out in the Bloomberg article certainly is plausible in theory, but without any of the so-called 'spy chips,' the story has zero merit with me," Moorhead told Security Now. "It's like having a hold up at a bank and no one has any evidence of guns or even any damage being done or anything stolen. This story should be retracted."
While the third-party that did the investigation was not named in the letter, Reuters reported that Nardello & Co conducted the review.
In the letter, the executives note that the complexity of the Supermicro's motherboard designs make it difficult or impossible for someone to tamper with the hardware. Also, the company's notes that no single employee or outside contractor is given unrestricted access to the board designs.
Related posts:
— Scott Ferguson is the managing editor of Light Reading and the editor of Security Now. Follow him on Twitter @sferguson_LR.
Read more about:
Security NowAbout the Author
You May Also Like
Uncovering Threats to Your Mainframe & How to Keep Host Access Secure
Feb 13, 2025Securing the Remote Workforce
Feb 20, 2025Emerging Technologies and Their Impact on CISO Strategies
Feb 25, 2025How CISOs Navigate the Regulatory and Compliance Maze
Feb 26, 2025Where Does Outsourcing Make Sense for Your Organization?
Feb 27, 2025




