Breaking cybersecurity news, news analysis, commentary, and other content from around the world, with an initial focus on the Middle East & Africa and the Asia Pacific
Bug Bounty Programs, Hacking Contests Power China's Cyber OffenseBug Bounty Programs, Hacking Contests Power China's Cyber Offense
With the requirement that all vulnerabilities first get reported to the Chinese government, once-private vulnerability research has become a goldmine for China's offensive cybersecurity programs.
June 18, 2024

China's cybersecurity experts over the past decade have evolved from hesitant participants in global capture-the-flag competitions, exploit contests, and bug bounty programs to dominant players in these arenas — and the Chinese government is applying those spoils toward stronger cyber-offensive capabilities for the nation.
In 2014, for example, Keen Team was the sole Chinese hacking group to take home a prize — scoring 13% of the purse — from the Pwn2Own exploit contest. But by 2017, seven China-based teams collected 79% of the prize money from the contest, according to data from the report, "From Vegas to Chengdu Hacking Contests, Bug Bounties, and China's Offensive Cyber Ecosystem," published last week. The following year, China banned participation in Western contests, gauging the vulnerability information too important to national security.
Its civilian hackers have directly benefited China's cyber-offensive programs and are one example of the success of China's cybersecurity pipeline, which the government created through its requirement that all vulnerabilities be directly reported to government authorities, says Eugenio Benincasa, senior researcher at the Center for Security Studies (CSS) at ETH Zurich, and the author of the report.
"By strategically positioning itself as the final recipient in the vulnerability disclosure processes of civilian researchers, the Chinese government leverages its civilian vulnerability researchers, among the best globally, on a large scale and at no cost," he says.
The open source intelligence report comes as the United States, Australia, Japan, South Korea, and other nations in the Asia-Pacific region have struggled to improve cyber defenses against Chinese advance persistent threat (APT) groups. Earlier this year, high-profile US government officials warned that China was compromising critical infrastructure to pre-position its military hackers for future conflicts. And, in the recently uncovered "Operation Crimson Palace," three different threat teams in China conducted coordinated attacks against a Southeast Asia government agency.
A Robust Cyber Pipeline
Starting with university capture-the-flag competitions and ending with exploits that enable military cyber operations, China's pipeline for training civilian hackers highlights the benefits of the country's focus on practical cybersecurity. China's cyber-offensive capability has also significantly benefited from the enforcement of its vulnerability disclosure rule, the Regulations on the Management of Security Vulnerabilities in Network Products (RMSV). Both programs are part of China's overall Military-Civil Fusion (MCF) initiative.
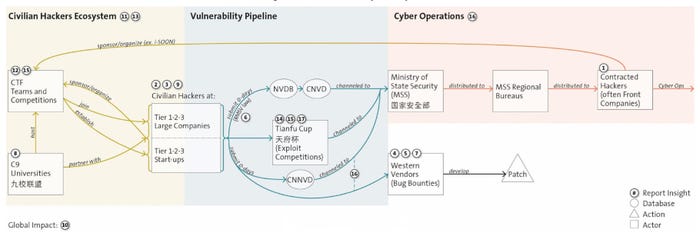
Flow chart showing the pipeline for cybersecurity expertise and vulnerability information. Source: ETH Zurich's "From Vegas to Chengdu Hacking Contests, Bug Bounties, and China’s Offensive Cyber Ecosystem" paper
Focusing its burgeoning numbers of technical graduates on finding vulnerabilities helps amplify its offensive capabilities, says Chris Wysopal, chief technology officer at software security firm Veracode.
"There is a scale difference there. ... They have a large number of technical graduates, and that is being harnessed to find vulnerabilities in [Western products, such as] Google Android," he says. "This shows that the incentives are working in their favor, and there's evidence of that."
Two groups of hackers exist within China's cyber-offensive ecosystems. The first group includes vulnerability researchers and offensive security specialists who have distinguished themselves by competing in bug bounty programs and hacking contests, such as the Pwn2Own contest and the Tianfu Cup, which was established as a China-based alternative to Pwn2Own.
The second group consists of the contracted or professional hackers who weaponize vulnerabilities for use in attacks on specific targets. Exploits developed by the first group have often been used by the second, a fact discussed in the iSoon leak earlier this year.
In the past, vulnerability research teams were typically associated with technical groups at large firms, such as Qihoo 360, which has at least 19 teams; the Ant Group, which hosts nine teams; and Tencent, which has at least seven research groups. Today, the researchers often are part of boutique cybersecurity firms.
China's civilian hackers initially obtained training by participating in Western capture-the-flag contests and exploit-development competitions, such as Pwn2Own, as well as bug bounty programs. China now has domestic versions of most of these initiatives and programs, often with the financial backing of top-tier national technical universities.
Cybersecurity Superstars
A handful of researchers have made significant contributions to China's programs, highlighting China's reliance on a small group of researchers, according to the report.
More than 50% of Google Android vulnerabilities, for example, are credited to Qihoo 360's Security Response Center (360 SRC), naming Han Zinuo as one of the contributors. When Zinuo moved to cybersecurity firm Oppo, 360 SRC's submissions dropped and Oppo's increased, the research paper stated. Similarly, another researcher, Yuki Chen, accounted for 68% of Qihoo 360's Vulcan researcher group's submissions to Microsoft, and when he moved to boutique firm Cyber Kunlun in 2020, the former firm saw a significant drop in vulnerabilities to Microsoft's bug bounty program, while the latter saw a surge.
Overall, the number of vulnerabilities reported by Chinese firms to the big three US software companies — Apple, Google, and Microsoft — declined starting in 2020. While this could suggest that Chinese firms were no longer reporting the vulnerabilities they discovered, it also coincided with increasing sanctions from the United States, such as the blacklisting of Qihoo 360 in May 2020 due to its links to the Chinese military, the report stated.
"This decrease [in vulnerability reports has] raised concerns about the potential loss of a significant channel for vulnerability reporting within the global ecosystem," the report said.
Downsides for Defense
Because Chinese teams have curtailed their participation in Western hacking competitions, they have arguably made the competitions less effective as a defensive strategy. In 2022 and 2023, for example, no teams attempted to hack either Apple's iPhone or Google's Pixel at the Pwn2Own competition — that was the first time in 15 years for Apple's iPhone — indicating that China now considers any exploits its experts find as too valuable to demonstrate publicly.
"The notable absence of Chinese hacking teams that specialized in targeting these devices explains this break far better than assuming that the iPhone and Pixel have become unbreachable," the research paper stated. "Concurrently, these vulnerabilities are highly likely evaluated by China's security agencies for potential use in cyber malicious operations."
Even showing such exploits without any accompanying details runs the risk of directing attackers to rediscover vulnerabilities, says Dustin Childs, head of threat awareness for the Zero Day Initiative at Trend Micro, which runs the Pwn2Own competition.
"They have already been demonstrated onstage, so threat actors know they aren’t wasting their time reversing a patch for some that may end up non-exploitable," he says. "This is why we invite vendors to participate in the contest."
Private organizations that deal in exploits act as a bellwether for the vulnerability market. Exploit seller Zerodium currently offers a $2.5 million payday for any hacker that finds a zero-click exploit chain for Google Android and $2 million for a similar attack on iOS.
China's Own Hacking Competitions
Meanwhile, China is further divorcing itself from the global information infrastructure, moving its infrastructure to domestically developed technology. Unsurprisingly, its cybersecurity pipeline is following suit, with some major exploit competitions focusing increasingly on Chinese products.
In the long term, China will have to follow two paths, Benincasa says.
"We are observing an interesting shift in China's hacking competitions toward focusing more on their own products, while at the same time maintaining a strong interest in Western ones," he says, adding, "China's strategic intent [is] to maintain a presence in international products for offensive purposes, given the expertise of its hackers in targeting Western products, while simultaneously focusing on domestic products for defensive purposes as it gradually reduces reliance on US vendors."
Read more about:
CISO CornerAbout the Author
You May Also Like