QR Code 'Quishing' Attacks on Execs Surge, Evading Email SecurityQR Code 'Quishing' Attacks on Execs Surge, Evading Email Security
The use of QR codes to deliver malicious payloads jumped in Q4 2023, especially against executives, who saw 42 times more QR code phishing than the average employee.
February 8, 2024

Email attacks relying on QR codes surged in the last quarter, with attackers specifically targeting corporate executives and managers, reinforcing recommendations that companies place additional digital protections around their business leadership.
Making matters worse, phishing emails using QR codes (aka "quishing") can often get by spam filters, with attacks targeting users of Microsoft 365 and DocuSign successfully landing in email inboxes, according to a report published this week by Abnormal Security, a provider of cloud email security.
In the fourth quarter of 2023, the average top executive in the C-suite saw 42 times more phishing attacks using QR codes compared to the average employee. Other managerial roles suffered an increase in attacks as well, although significantly smaller, with these non-C-suite executives encountering five times more QR-code-based phishing attacks, according to the company's report.
Overall, the data demonstrates that attackers have executives — and other privileged users — in their sites, says Mike Britton, CISO for Abnormal Security.
"If I'm an attacker, I want to attack the people that have the ability for me to get paid and have credentials that give me access to the most interesting information," he says. "Or I want to pretend to be those people, because once again, social engineering requires that trust, [for a victim to think,] hey, this VP of sales or this VP of HR is asking me to do something, [making them] typically more likely ... to take action."
While QR codes have been around for three decades, they became much more popular during the pandemic, as restaurants and other businesses directed customers to contact-free and online ordering. In a business context, a top use case for QR codes is offering links to ease the sign-up process for multifactor authentication (MFA). Cyberattackers have hopped on: More than a quarter of QR code attacks (27%) in Q4 were fake notices of MFA, for example, while about one-in-five attacks (21%) were fake notifications about a shared document, according to Abnormal Security's report.
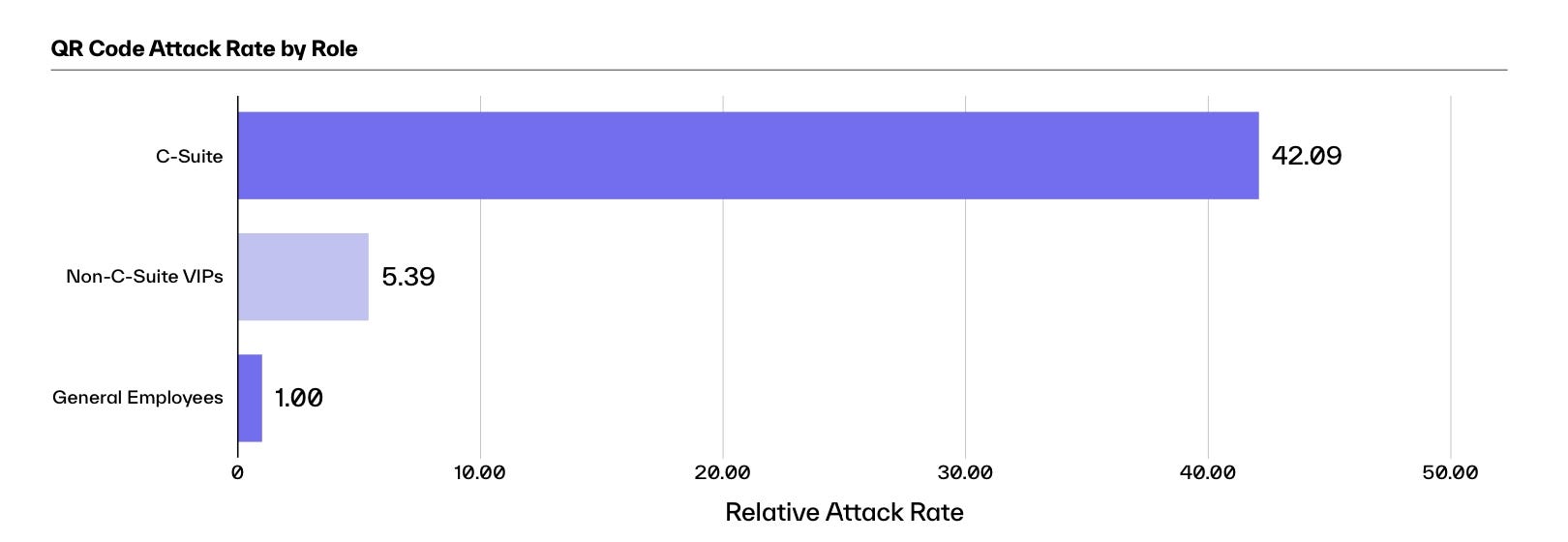
Top executives see 42 times more attacks using QR codes than regular employees. Source: Abnormal Security
Because attackers hide their phishing link in an image, QR code phishing bypasses user suspicions and some email security products. In addition, malicious QR codes can be placed in physical spaces using a simple sticker, bypassing digital security altogether.
"Attacks exploit users' inherent trust in QR codes, embedding them in everyday items like parking meters or posters," says Monique Becenti, director of product at mobile-security firm Zimperium. "The success rate of phishing with QR codes will surpass traditional phishing methods because they often bypass users' typical suspicion triggers, such as typos in the URL, leading to a higher likelihood of scanning them."
Yet Another Way to Steal Exec's Credentials
For the most part, quishing attackers who focus on executives are after the credentials — usernames and passwords — of privileged users. Credential phishing is the most popular form of email attack, accounting for 73% of all attacks through the vector and 84% of attacks using a QR code; and they often lead to more significant compromises, says Abnormal Security's Britton.
"The primary goal is getting at a user to steal their credentials," he says. "Once I have your credentials, I can do a lot more damage, and I can do a lot of lasting damage. If I have your credentials, I can log into your account, I can see who you've sent emails to, I can send emails pretending to be you, and I can create mail filter rules."
That last point is a common way to abuse mail credentials, Britton says. The attacker will create a blind carbon copy (BCC) rule that forwards all emails to the attacker's account.
Further, "threat actors also recognize that often multiple people have access to an executive's inbox, such as executive assistants," the report stated. "Consequently, every individual who knows the login credentials for a VIP's inbox represents a potential entry point that can be exploited by an attacker."
Thwarting Quishing Takes Technology & Training the Human
The good news is, since October, QR-code phishing has subsided to a large degree, after accounting for 22% of phishing attacks, according to human-risk management firm Hoxhunt. "Since last October, we've seen evidence that email filters are catching up to the QR phishing technique," says Jon Gellin, threat team lead at Hoxhunt. "As fewer of these attacks are bypassing email filters, there's been a resultant decrease in their popularity."
However, even if quishing subsides, it will remain a tool for attackers, much in the way that shortened URLs and image spam continue to be used in cyberattacks. The best way to protect users is to train them, Gellin says. About 5% of users respond to a phishing attack within the first few minutes, suggesting that a well-trained pool of employees can help blunt an attack.
"As the QR phishing trend has shown, some threats will always slip past even the most sophisticated filters," he says. "At that point, it's up to the human layer to have the skills and tools to deal with the threat effectively."
Training is important, but because a single failure can have a significant impact, technical controls are necessary, says Abnormal Security's Britton.
"There, there are some phishing attacks that I've seen that even I have to get a second opinion from people because they look so real," he says. "How do I expect an HR person to get that right every time? How do I expect an accounts payable person? How do I expect a financial analyst?"
"Training is important, but we're going to fail, and it only takes one failure," he says.
About the Author
You May Also Like
Uncovering Threats to Your Mainframe & How to Keep Host Access Secure
Feb 13, 2025Securing the Remote Workforce
Feb 20, 2025Emerging Technologies and Their Impact on CISO Strategies
Feb 25, 2025How CISOs Navigate the Regulatory and Compliance Maze
Feb 26, 2025Where Does Outsourcing Make Sense for Your Organization?
Feb 27, 2025



_vska_Alamy_.jpg?width=700&auto=webp&quality=80&disable=upscale)
_Brain_light_Alamy.jpg?width=700&auto=webp&quality=80&disable=upscale)