Person pushing a compliance button._NicoElNino_Alamy.jpg?width=700&auto=webp&quality=80&disable=upscale)
Cyber Risk_NicoElNino_Alamy.jpg?width=700&auto=webp&quality=80&disable=upscale)
Don't Forget to Report a Breach: A Cautionary TaleDon't Forget to Report a Breach: A Cautionary Tale
Responding to an incident quickly is important, but it shouldn't come at the expense of reporting it to the appropriate regulatory bodies.

Ask the Experts
Read MoreFEATURED THREAT MONITOR
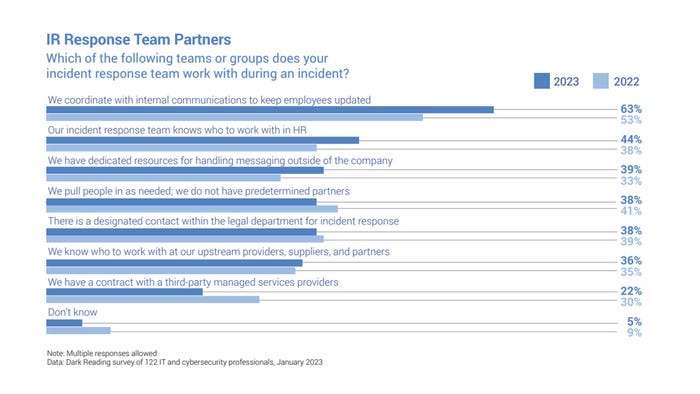
Effective Incident Response Relies on Internal and External Partnerships
Dark Reading research finds increased collaboration between security incident responders and groups within the HR, legal, and communications functions.







_NicoElNino_Alamy.jpg?width=300&auto=webp&quality=80&disable=upscale)